DevOps security: how modern teams build secure delivery pipelines
Cloud Security, Reliability & Governance
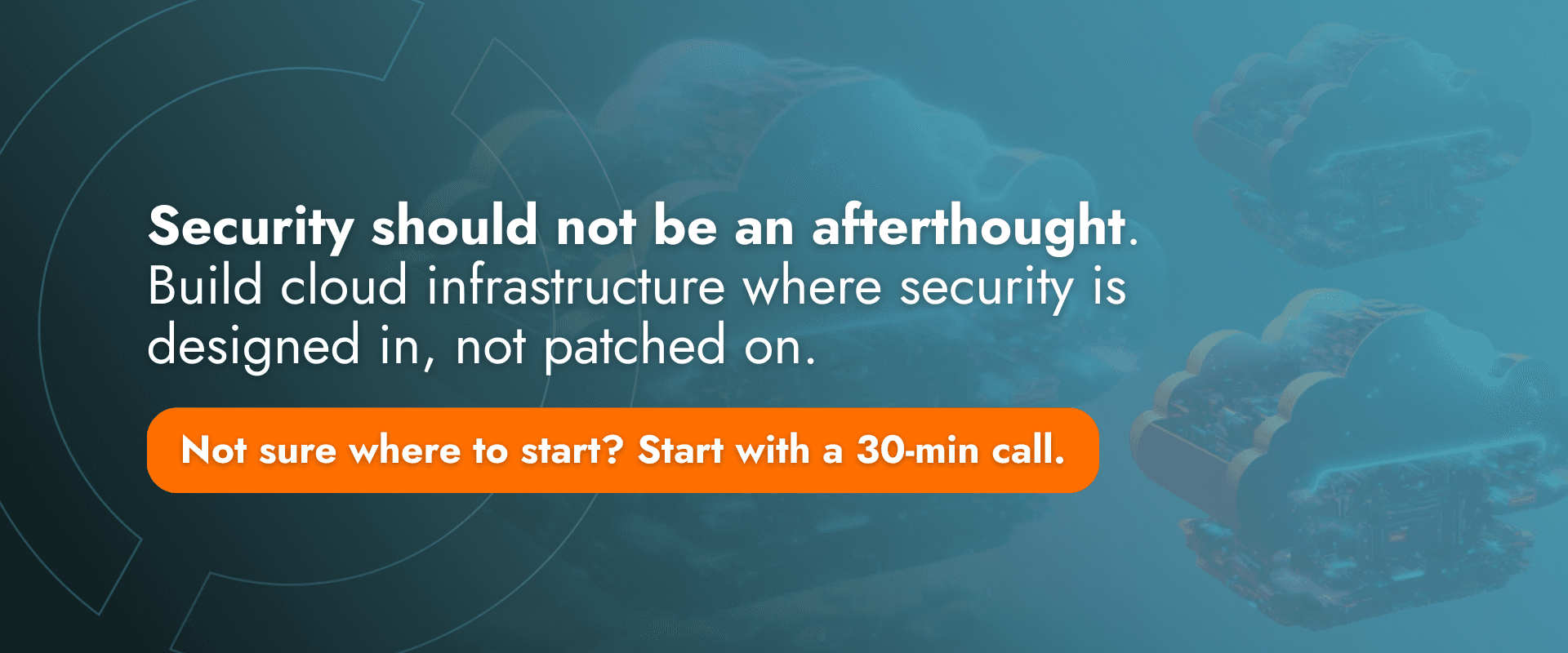
Modern engineering teams no longer treat security as a final checkpoint; instead, they embed it directly into DevOps workflows so protection becomes part of how systems are built and deployed.
This guide explains how DevOps security evolved into DevSecOps and why secure delivery pipelines are essential in cloud-native environments, covering key layers such as identity management, infrastructure validation, automated security testing, and runtime monitoring.
Why DevOps security matters more than ever
Over the last decade, the way software is built and delivered has changed dramatically. Applications that were once deployed a few times per year through carefully scheduled release windows are now delivered continuously through automated pipelines, while infrastructure itself is provisioned through code and managed inside highly dynamic cloud environments.
In this new operational landscape, containers are recreated frequently, services scale automatically, and infrastructure components evolve constantly; as a result, the attack surface of modern systems has expanded far beyond what traditional security models were designed to protect.
Every delivery pipeline introduces potential entry points. Automated processes interact with credentials, infrastructure APIs, and external services, while cloud platforms expose identity layers, networking boundaries, and management interfaces that must all be secured carefully.
Older development models handled security through late-stage reviews. Code audits happened shortly before release, infrastructure was managed manually by specialized teams, and deployment windows were relatively rare. That model worked when change moved slowly.
However, when deployments occur dozens, or even hundreds, of times per day, security can no longer be treated as a final inspection stage. It must be integrated directly into the delivery pipeline.
This shift, driven by automation, cloud infrastructure, and continuous delivery, ultimately led to the emergence of DevSecOps.
Understanding DevSecOps: security as part of delivery
DevSecOps is often described as the integration of security into DevOps workflows; while technically correct, that description only scratches the surface of what has actually changed inside modern engineering organizations.
DevSecOps is not simply about adding security tools to CI/CD pipelines. Instead, it reflects a deeper redesign of the delivery process, where security becomes part of how systems are built, validated, and operated from the beginning.
Rather than positioning security as a gate at the end of development, DevSecOps distributes security checks throughout the entire lifecycle of software delivery. Code is analyzed during development, dependencies are scanned before builds, infrastructure is validated before provisioning, automated vulnerability tests run during integration, and monitoring systems watch for anomalies after deployment.
Each of these checkpoints reduces risk earlier in the lifecycle. The principle behind this approach is straightforward: the earlier a vulnerability is detected, the easier and cheaper it becomes to resolve.
When security is embedded directly into development workflows, teams no longer face the traditional trade-off between speed and safety. Security stops being an external control mechanism and becomes part of everyday engineering practice.
The modern secure delivery pipeline
A secure delivery pipeline combines automation, policy enforcement, and system visibility across multiple stages of software delivery. While implementations vary across organizations, most modern pipelines share a similar architecture built around several complementary security layers.
1. Secure development practices
Security begins long before code enters a deployment pipeline. Developers must follow secure coding practices and rely on development environments capable of identifying vulnerabilities early in the process.
Many modern development workflows integrate static analysis tools that scan source code for common security issues such as hardcoded credentials, unsafe input validation, weak cryptographic implementations, or injection vulnerabilities. Because these checks occur while code is being written, engineers can resolve problems immediately while the context of the change is still clear.
Dependency management represents another critical area. Modern applications depend heavily on open-source libraries, which accelerate development but can also introduce supply-chain risk when vulnerabilities are discovered. Tools that scan dependencies for known security issues allow teams to monitor risks across the entire software stack.
By integrating these checks directly into development workflows, organizations significantly reduce the likelihood that vulnerable components reach production environments.

2. Secure CI/CD pipelines
Continuous Integration and Continuous Delivery pipelines automate the building, testing, and deployment of software; because they interact directly with infrastructure and credentials, they represent one of the most sensitive components of any DevOps environment.
For this reason, pipeline access must be tightly controlled through identity management and role-based permissions, ensuring that only authorized users and services can trigger deployments or modify pipeline configurations.
Secrets management is equally critical. API keys, database credentials, and infrastructure tokens should never be stored inside source repositories or configuration files; instead, they must be managed through dedicated secrets platforms capable of encrypting, rotating, and auditing access to sensitive data.
Secure pipelines also integrate automated security testing stages. These often include static application security testing (SAST), dynamic application security testing (DAST), software composition analysis (SCA), and container vulnerability scanning.
When these checks run automatically inside CI/CD pipelines, vulnerabilities can be detected before deployments reach production, allowing teams to maintain fast delivery cycles while enforcing consistent security standards.
3. Infrastructure as Code security
Infrastructure as Code has become a fundamental part of modern DevOps environments. Tools such as Terraform, CloudFormation, and Pulumi allow teams to define infrastructure configurations through version-controlled code, ensuring consistency and reproducibility across environments.
However, IaC also introduces new security risks. Misconfigured templates can expose services publicly, grant excessive permissions, or deploy insecure network configurations.
To mitigate these risks, many organizations use IaC scanning tools that analyze infrastructure definitions before deployment. These tools detect issues such as open security groups, unencrypted storage volumes, overly permissive IAM policies, or publicly exposed databases.
Because infrastructure definitions pass through the same pipelines as application code, these checks can be enforced automatically. As a result, infrastructure security becomes part of the delivery process rather than a separate operational concern.

Identity and access management
In cloud-native systems, identity has become one of the most important security layers. Traditional architectures relied heavily on network boundaries; however, distributed cloud environments operate through APIs, services, and automated workflows that interact continuously.
Because of this shift, access control must be enforced primarily through identity rather than network location.
Modern DevOps security strategies rely on the principle of least privilege: every service, engineer, and automation process receives only the permissions required to perform its tasks. Identity systems typically include role-based access control, short-lived credentials, federated authentication mechanisms, and detailed audit logs that track every access event.
Many organizations complement these mechanisms with a Zero Trust model, where no system is automatically trusted based on network location alone. Instead, every request must be authenticated, authorized, and logged, significantly reducing the risk of lateral movement if a system becomes compromised.
Runtime monitoring and observability
Even when strong security practices are implemented during development and deployment, risks still exist once systems begin operating in production environments. Runtime monitoring therefore plays a critical role in detecting suspicious behavior and identifying potential security incidents early.
Modern observability platforms collect signals from multiple sources, including application logs, system metrics, network activity, and user behavior. Security monitoring systems analyze these signals to identify anomalies such as unexpected privilege escalations, unusual API activity, unauthorized access attempts, or abnormal network traffic patterns.
Because these signals are analyzed continuously, engineering teams gain early visibility into potential threats and can respond quickly when unusual behavior appears.
By integrating security monitoring with observability platforms, organizations gain a unified view of both system health and operational risk.
FAQ: DevOps security and secure CI/CD pipelines
What is DevOps security?
DevOps security refers to integrating security practices directly into development, deployment, and operations workflows so vulnerabilities can be identified and addressed continuously throughout the software lifecycle.
What is DevSecOps?
DevSecOps extends DevOps by embedding security controls across the entire delivery pipeline, including development environments, CI/CD pipelines, infrastructure provisioning, and runtime monitoring.
How do you secure a CI/CD pipeline?
A secure CI/CD pipeline typically includes identity-based access control, secure secrets management, automated security testing, infrastructure validation, and policies that prevent insecure deployments.
What are the most common DevSecOps vulnerabilities?
Common issues include exposed credentials, misconfigured cloud infrastructure, insecure dependencies, overly permissive identity permissions, and insufficient monitoring of runtime environments.
Why is DevOps security important in cloud environments?
Cloud infrastructure is dynamic and highly automated; without integrated security practices, vulnerabilities can spread quickly across systems and become difficult to detect.
What is the difference between DevOps and DevSecOps?
DevOps focuses on speed and automation in software delivery, while DevSecOps integrates security controls throughout the entire development and deployment lifecycle.
Final thoughts
Modern software delivery depends on automation, speed, and scalability; however, these same characteristics also introduce new security challenges that traditional protection models were never designed to handle.
DevOps security offers a practical framework for embedding protection directly into the engineering lifecycle. By combining secure development practices, automated security testing, identity management, infrastructure protection, and runtime monitoring, organizations can build delivery pipelines that support both velocity and resilience.
Ultimately, secure DevOps pipelines are not defined by the tools they use but by the engineering practices they enable. When security becomes part of how systems are designed, deployed, and operated, teams can innovate confidently without exposing their infrastructure to unnecessary risk.


EZOps Cloud delivers secure and efficient Cloud and DevOps solutions worldwide, backed by a proven track record and a team of real experts dedicated to your growth, making us a top choice in the field.
EZOps Cloud: Cloud and DevOps merging expertise and innovation